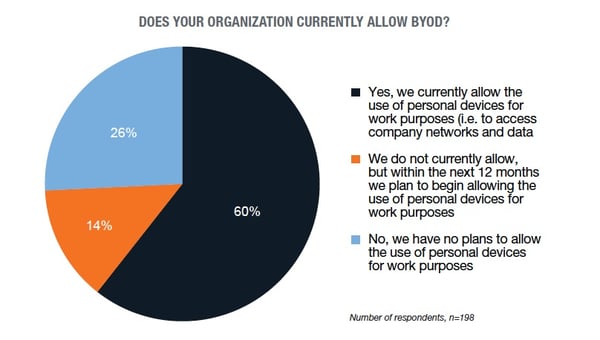
Did you know that more than 74 percent of U.S. businesses either have a bring-your-own-device (BYOD) policy or plan to have one in place within 12 months? Sixty-seven percent of U.S. workers report using their own mobile devices at work, and the majority of those devices are smartphones. There are currently over 230 million smartphone users in the U.S., and that number is expected to grow to 270.66 million by 2022.
The more mobile devices become part of the workplace, the more Connecticut companies have to worry about mobile security threats. For example, mobile banking Trojan attacks peaked at more than 61,000 – an all-time high – in the second quarter of 2018. One in five Android phones experienced a mobile threat in 2014. And according to Symantec’s Internet Security Threat Report 2018 third-party app stores hosted 99.9 percent of discovered mobile malware. While mobile computing is growing in popularity, security is not keeping pace.
How are you going to head off mobile security threats for your business? Here are some considerations and strategies to head off security issues related to BYOD.
The Source of Mobile Security Threats
When considering how to develop a secure BYOD strategy, remember that smartphones are consumer devices—they were not designed to serve as portable workstations. As consumer technology is being adapted for business use, IT professionals have to develop new security strategies. Smartphones are vulnerable to attacks in various ways:
1. Lack of Security Software
Smartphones are connected to the internet via wireless networks, cellular networks, or USB connections. Any of these connections can transfer malware. Viruses can even be transmitted via Bluetooth. Consider adopting a mobile data security suite as part of your arsenal. Trend Micro, Kaspersky, Norton, and other security software vendors all offer smartphone anti-malware solutions.
2. Small-Screen Surfing
Smartphone web browsers are becoming more user-friendly, but they also can be gateways for an attack. Small screens make it harder to spot a phishing site, and malware can be transferred before a threat is detected. One solution is to adopt firewall software that performs deep packet inspection to prevent transfer of malware.
3. Wi-Fi Vulnerability
Connecting to an unsecured network may be the biggest vulnerability for smartphones. In addition to 3G and 4G cellular connections, smartphones are equipped with Wi-Fi, which can be very useful for data transfer over a secure network. However, using open Wi-Fi connections at the local coffee shop makes proprietary information stored on the phone, such as passwords, vulnerable. The best strategy is to provide an encrypted data link back to the company network using an SSL VPN so that data in transit is encrypted.
4. Security Bypass
Some phones have built-in data security bypasses to simplify things for the user. For example, on an Android phone, you can access an Exchange Server by accepting all SSL certificates. Be sure to use secure system settings and strategies such as two-factor authentication for added security.
5. Physical Security
Smartphones tend to be lost or stolen. People also lend their phones from time to time. Be sure that users enable basic security on their devices, such as a PIN or password protection, or, better yet, fingerprint authentication.
Best Practices for Mobile Security
When dealing with enterprise mobile security, you really have no control over mobile devices. While smartphones promote productivity, they also are moving targets that can be impossible to manage. They are outside the corporate firewall threat management, and enterprise security systems, so your best defense is educating users about potential threats and implementing back-end strategies to protect data in the field. Here are some best practices to stave off mobile security threats:
1. Insist on Mobile Malware Protection
As part of BYOD policy, every smartphone should be equipped with mobile malware protection. You also should have remote access to smartphones so that you can wipe the data if the phone is lost or stolen.
2. Use Strong Authentication
Secure your enterprise systems with encrypted data and strong password protection. Use passwords that are hard to guess, and change them regularly. Consider locking users out after three unsuccessful remote log-in attempts.
3. Create Separate, Secured Mobile Gateways
Route smartphone and mobile data traffic through special gateways with customized firewalls and security. This makes it easier to control remote user access and isolate sensitive data that shouldn’t be accessible by remote devices.
4. Control Risk from Third-Party Software
Because smartphones are personal devices, corporate IT managers can’t control installation of third-party software. You can adopt policies to limit or block use of third-party software to prevent installations of rogue software with back doors and Trojans. Using a remote virtual work environment provides protection, because remote users only get screen output rather than actual data transfers.
5. Use Over-the-Air Security Updates
You can’t count on users to keep smartphone software up to date. Use transmitted software updates to be sure that applications have the latest bug and security fixes.
6. Perform Regular Security Audits
Audit your security system regularly to make sure software and protocols are up to date. Also, consider hiring an outside security firm to perform annual penetration testing to identify weaknesses.
7. Train your Staff
Even though smartphone use can increase productivity, BYOD should be considered a privilege with its own responsibilities. Be sure to establish strict protocols and procedures to promote secure remote data access, and train your team members in how to use their smartphones safely for work.
As you embrace BYOD strategies to support roving employees and telecommuters, security has to be a primary consideration. If you aren’t sure where to start or how to be sure your enterprise is secure for smartphone users, ask for professional advice. Managed Services Providers (MSPs) like NSI are expert in developing secure, remote user strategies. It’s the MSP’s job to stay current with security vendors and procedures to make sure that customers’ data remains secure, whether access is from inside the firewall or via a smartphone. Save yourself the worry and get help from the experts.
Editor's Note: This post was originally published in November 2017, and has since been updated for accuracy.